Days after the Conti ransomware group broadcasted a pro-Russian message pledging its allegiance to Vladimir Putin's ongoing invasion of Ukraine, an anonymous security researcher using the Twitter handle @ContiLeaks has leaked the syndicate's internal chats.
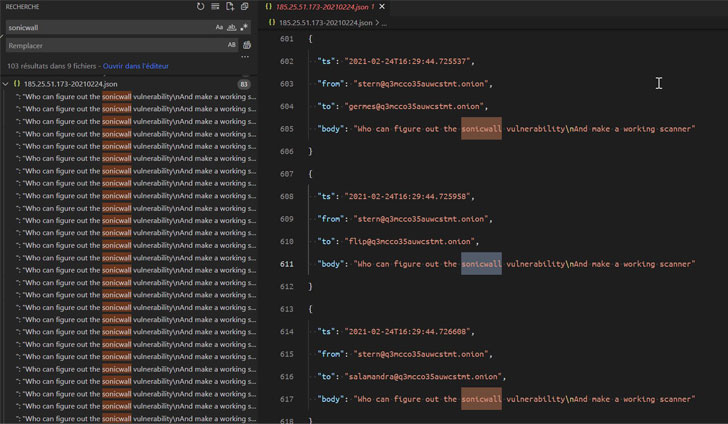
The file dump, published by malware research group VX-Underground, is said to contain 13 months of chat logs between affiliates and administrators of the Russia-affiliated ransomware group from June 2020 to February 2022, in a move that's expected to offer unprecedented insight into the criminal enterprise's inner workings.
"Glory to Ukraine," the leaker said in their message.
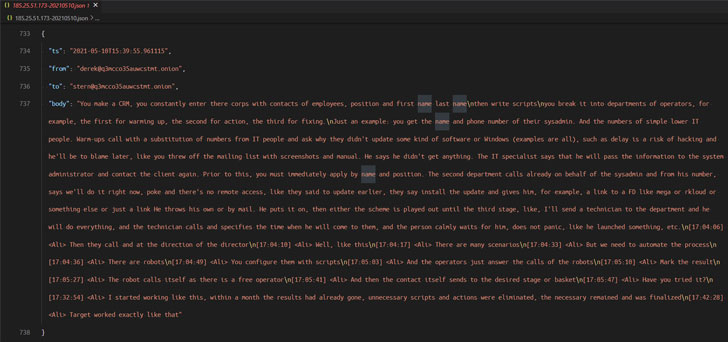
The shared conversations show that Conti used fake front companies to attempt to schedule product demos with security firms like CarbonBlack and Sophos to obtain code signing certificates, with the operators working in scrum sprints to complete the software development tasks.
Additionally, the messages confirm the shutdown of the TrickBot botnet last week as well as highlight the Conti group's close relationship with the TrickBot and Emotet malware gangs, the latter of which was resurrected late last year through TrickBot.
A message sent by one of the members of the group on February 14, 2022 goes: "TrickBot does not work. The project was closed."
On top of that, the leaker is also believed to have released the source code associated with TrickBot's command dispatcher and data collector modules, not to mention the ransomware group's internal documentation, its administrative panel, and a password-protected archive containing the source code for the decryptor and the builder.
 |
| Source: Émilio Gonzalez (@res260) |
 |
| Source: Émilio Gonzalez (@res260) |
The development comes as the Russo-Ukrainian conflict has splintered the cybercrime underground into two warring factions, with a growing number of hacking actors picking sides between the two countries on the digital front.
The Conti team, in a blog post on its dark web portal last week, avowed its "full support" to the Russian invasion, and threatened to retaliate against critical infrastructure if Russia is hit with cyber or military attacks.
It, however, later backtracked, saying, "we do not ally with any government and we condemn the ongoing war," but reiterated that "We will use our resources in order to strike back if the well being and safety of peaceful citizens will be at stake due to American cyber aggression."
Separately, a group of Belarusian hackers known as the Cyber Partisans stated they staged an attack on the country's train network in an effort to disrupt Russian troop movements into Ukraine, while another group called AgainstTheWest_ said it was "standing against Russia" and that it breached a number of websites and corporations.
The Anonymous, for its part, also claimed responsibility for disrupting the websites of state news agencies RT, TASS, and RIA Novosti, as well as websites of newspapers Kommersant, Izvestiya, and Forbes Russia magazine and the Russian oil giant Gazprom.
If anything, the rapidly evolving cyber war appears to have put other groups on alert, what with LockBit ransomware operators posting a neutral message, stating "For us it is just business and we are all apolitical. We are only interested in money for our harmless and useful work."
The string of "crowd sourced attacks" by vigilante hacker groups amidst intensifying Russian military attack on Ukraine presents a "new risk of crisis escalation," Matt Olney, director of threat intelligence and interdiction at Cisco Talos, said.
"The last seven days have created a wild environment of government entities, affiliated freelancers and semi-legitimate cyber strike actors and affiliates all driven out of righteous nationalistic anger," Olney added. "Governments are seeking volunteers to conduct cyberattacks against the opposition. This presents a huge global risk as the potential for hostile spill-over is immense."
- Get link
- X
- Other Apps
- Get link
- X
- Other Apps
Comments
Post a Comment