Cybersecurity researchers today took the wraps off a new sophisticated cyber-espionage campaign directed against aerospace and military organizations in Europe and the Middle East with an aim to spy on key employees of the targeted firms and, in some case, even to siphon money.
The campaign, dubbed “Operation In(ter)ception” because of a reference to "Inception" in the malware sample, took place between September to December 2019, according to a new report cybersecurity firm ESET shared.
"The primary goal of the operation was espionage," the researchers told The Hacker News. "However, in one of the cases we investigated, the attackers tried to monetize access to a victim's email account through a business email compromise (BEC) attack as the final stage of the operation."
The campaign, dubbed “Operation In(ter)ception” because of a reference to "Inception" in the malware sample, took place between September to December 2019, according to a new report cybersecurity firm ESET shared.
"The primary goal of the operation was espionage," the researchers told The Hacker News. "However, in one of the cases we investigated, the attackers tried to monetize access to a victim's email account through a business email compromise (BEC) attack as the final stage of the operation."
The financial motivation behind the attacks, coupled with similarities in targeting and development environment, have led ESET to suspect Lazarus Group, a notorious hacking group that's been attributed to working on behalf of the North Korean government to fund the country's illicit weapon and missile programs.
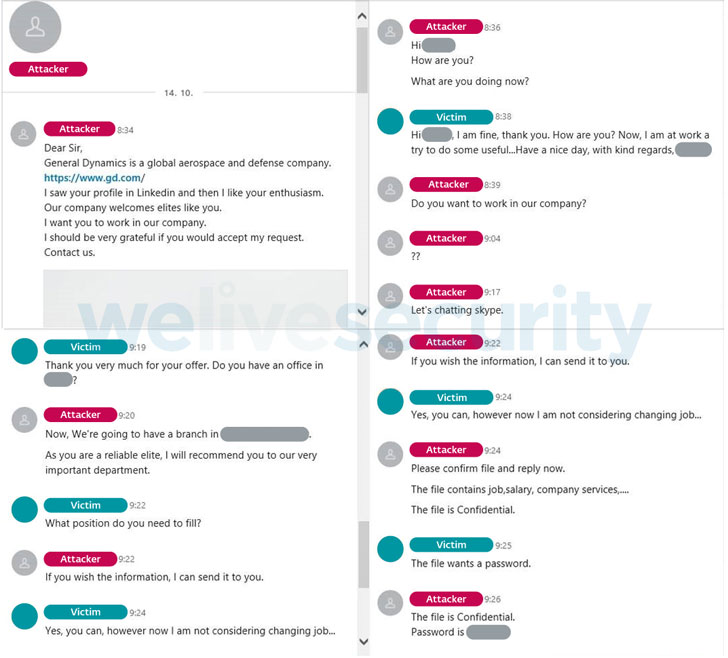
Stating that the campaign was highly targeted, ESET said it relied on social engineering tricks to lure employees working for the chosen companies with fake job offers using LinkedIn's messaging feature, posing as HR managers of well-known companies in the aerospace and defense industry, including Collins Aerospace and General Dynamics.
"Once the contact was established, the attackers snuck malicious files into the communication, disguising them as documents related to the advertised job offer," the researchers said, based on an investigation with two of the affected European companies.
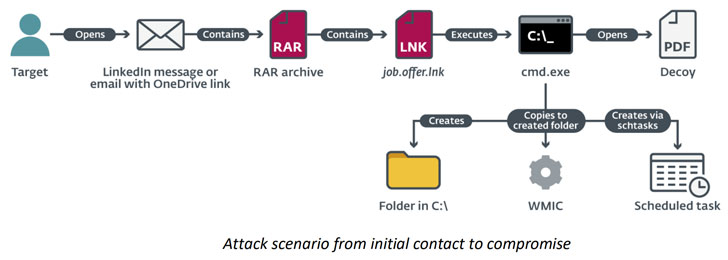
The decoy RAR archive files, which were directly sent over the chats or as emails sent from their fake LinkedIn personas pointing to an OneDrive link, purported to contain a PDF document detailing salary information of specific job positions, when in actuality, it executed Windows' Command Prompt utility to perform a series of actions:
The actors behind the operation, upon gaining an initial foothold inside the target company, went on to employ a custom malware downloader, which in turn downloaded a previously undocumented second-stage payload — a C++ backdoor that periodically sends requests to an attacker-controlled server, carry out pre-defined actions based on the received commands, and exfiltrate the collected information as a RAR file via a modified version of dbxcli, an open-source command-line client for Dropbox.
In addition to using WMIC to interpret remote XSL scripts, the adversaries also abused native Windows utilities such as "certutil" to decode base64-encoded downloaded payloads, and "rundll32" and "regsvr32" to run their custom malware.
"We actively seek out signs of state-sponsored activity on the platform and quickly take action against bad actors in order to protect our members. We don't wait on requests, our threat intelligence team removes fake accounts using information we uncover and intelligence from a variety of sources, including government agencies," Paul Rockwell, Head of Trust and Safety at LinkedIn said in a statement sent to The Hacker News.
"Our teams utilize a variety of automated technologies, combined with a trained team of reviewers and member reporting, to keep our members safe from all types of bad actors. We enforce our policies, which are very clear: the creation of a fake account or fraudulent activity with an intent to mislead or lie to our members is a violation of our terms of service. In this case, we uncovered instances of abuse that involved the creation of fake accounts. We took immediate action at that time and permanently restricted the accounts"
Besides reconnaissance, ESET researchers also found evidence of attackers attempting to exploit the compromised accounts to extract money from other companies.
Although unsuccessful, the monetization tactic worked by using the existing email communications between the account holder and a customer of the company to settle an outstanding invoice to a different bank account under their control.
"As part of this ruse, the attackers registered an identical domain name to that of the compromised company, but on a different top-level domain, and used an email associated with this fake domain for further communication with the targeted customer," ESET said.
Ultimately, the targeted customer reached out to the correct email address of the victim about the suspicious emails, thus foiling the attackers' attempt.
"Our research into Operation In(ter)ception shows again how effective spear-phishing can be for compromising a target of interest," the researchers concluded.
"They were highly targeted and relied on social engineering over LinkedIn and custom, multistage malware. To operate under the radar, the attackers frequently recompiled their malware, abused native Windows utilities, and impersonated legitimate software and companies."
Social Engineering via LinkedIn.
Stating that the campaign was highly targeted, ESET said it relied on social engineering tricks to lure employees working for the chosen companies with fake job offers using LinkedIn's messaging feature, posing as HR managers of well-known companies in the aerospace and defense industry, including Collins Aerospace and General Dynamics.
"Once the contact was established, the attackers snuck malicious files into the communication, disguising them as documents related to the advertised job offer," the researchers said, based on an investigation with two of the affected European companies.
The decoy RAR archive files, which were directly sent over the chats or as emails sent from their fake LinkedIn personas pointing to an OneDrive link, purported to contain a PDF document detailing salary information of specific job positions, when in actuality, it executed Windows' Command Prompt utility to perform a series of actions:
- Copy Windows Management Instrumentation command-line tool (wmic.exe) to a specific folder
- Rename it to something innocuous to evade detection (e.g., Intel, NVidia, Skype, OneDrive and Mozilla), and
- Create scheduled tasks that execute a remote XSL script via WMIC.
The actors behind the operation, upon gaining an initial foothold inside the target company, went on to employ a custom malware downloader, which in turn downloaded a previously undocumented second-stage payload — a C++ backdoor that periodically sends requests to an attacker-controlled server, carry out pre-defined actions based on the received commands, and exfiltrate the collected information as a RAR file via a modified version of dbxcli, an open-source command-line client for Dropbox.
In addition to using WMIC to interpret remote XSL scripts, the adversaries also abused native Windows utilities such as "certutil" to decode base64-encoded downloaded payloads, and "rundll32" and "regsvr32" to run their custom malware.
"We actively seek out signs of state-sponsored activity on the platform and quickly take action against bad actors in order to protect our members. We don't wait on requests, our threat intelligence team removes fake accounts using information we uncover and intelligence from a variety of sources, including government agencies," Paul Rockwell, Head of Trust and Safety at LinkedIn said in a statement sent to The Hacker News.
"Our teams utilize a variety of automated technologies, combined with a trained team of reviewers and member reporting, to keep our members safe from all types of bad actors. We enforce our policies, which are very clear: the creation of a fake account or fraudulent activity with an intent to mislead or lie to our members is a violation of our terms of service. In this case, we uncovered instances of abuse that involved the creation of fake accounts. We took immediate action at that time and permanently restricted the accounts"
Financially Motivated BEC Attacks.
Besides reconnaissance, ESET researchers also found evidence of attackers attempting to exploit the compromised accounts to extract money from other companies.
Although unsuccessful, the monetization tactic worked by using the existing email communications between the account holder and a customer of the company to settle an outstanding invoice to a different bank account under their control.
"As part of this ruse, the attackers registered an identical domain name to that of the compromised company, but on a different top-level domain, and used an email associated with this fake domain for further communication with the targeted customer," ESET said.
Ultimately, the targeted customer reached out to the correct email address of the victim about the suspicious emails, thus foiling the attackers' attempt.
"Our research into Operation In(ter)ception shows again how effective spear-phishing can be for compromising a target of interest," the researchers concluded.
"They were highly targeted and relied on social engineering over LinkedIn and custom, multistage malware. To operate under the radar, the attackers frequently recompiled their malware, abused native Windows utilities, and impersonated legitimate software and companies."
THN
#osutayusuf
- Get link
- X
- Other Apps
- Get link
- X
- Other Apps

Comments
Post a Comment