Remember Strandhogg?
A security vulnerability affecting Android that malicious apps can exploit to masquerade as any other app installed on a targeted device to display fake interfaces to the users, tricking them into giving away sensitive information.
Late last year, at the time of its public disclosure, researchers also confirmed that some attackers were already exploiting the flaw in the wild to steal users' banking and other login credentials, as well as to spy on their activities.
The same team of Norwegian cybersecurity researchers today unveiled details of a new critical vulnerability (CVE-2020-0096) affecting the Android operating system that could allow attackers to carry out a much more sophisticated version of Strandhogg attack.
A security vulnerability affecting Android that malicious apps can exploit to masquerade as any other app installed on a targeted device to display fake interfaces to the users, tricking them into giving away sensitive information.
Late last year, at the time of its public disclosure, researchers also confirmed that some attackers were already exploiting the flaw in the wild to steal users' banking and other login credentials, as well as to spy on their activities.
The same team of Norwegian cybersecurity researchers today unveiled details of a new critical vulnerability (CVE-2020-0096) affecting the Android operating system that could allow attackers to carry out a much more sophisticated version of Strandhogg attack.
Dubbed 'Strandhogg 2.0,' the new vulnerability affects all Android devices, except those running the latest version, Android Q / 10, of the mobile operating system—which, unfortunately, is running on only 15-20% of the total Android-powered devices, leaving billions of rest of the smartphones vulnerable to the attackers.
StrandHogg 1.0 was resided in the multitasking feature of Android, whereas the new Strandhogg 2.0 flaw is basically an elevation of privilege vulnerability that allows hackers to gain access to almost all apps.
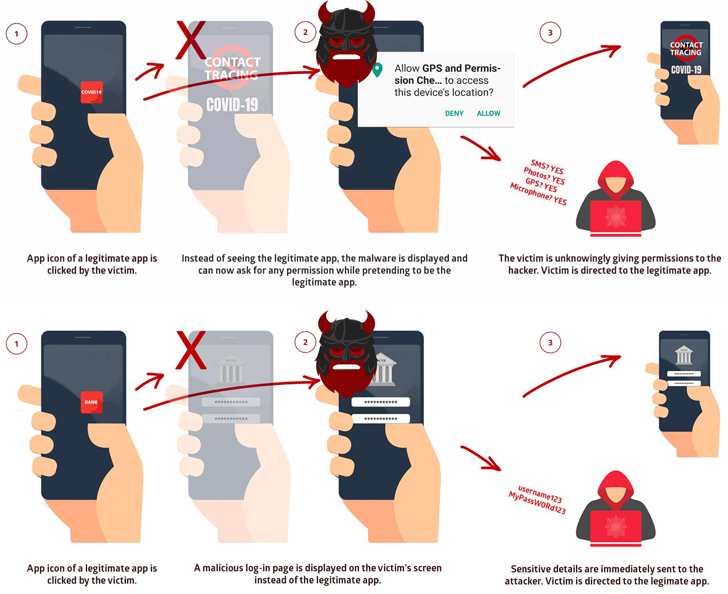
As explained before, when a user taps the icon of a legitimate app, the malware exploiting Strandhogg vulnerabilities can intercept and hijack this activity/task to display a fake interface to the user instead of launching the real application.
However, unlike StrandHogg 1.0 that can only attack apps one at a time, the latest flaw could let attackers "dynamically attack nearly any app on a given device simultaneously at the touch of a button," all without requiring a pre-configuration for each targeted app.
StrandHogg flaws are potentially dangerous and concerning because:
Besides stealing login credentials through a convincing fake screen, the malware app can also escalate its capabilities significantly by tricking users into granting sensitive device permissions while posing as a legitimate app.
"Utilising StrandHogg 2.0, attackers can, once a malicious app is installed on the device, gain access to private SMS messages and photos, steal victims' login credentials, track GPS movements, make and/or record phone conversations, and spy through a phone's camera and microphone," the researchers said.
StrandHogg 1.0 was resided in the multitasking feature of Android, whereas the new Strandhogg 2.0 flaw is basically an elevation of privilege vulnerability that allows hackers to gain access to almost all apps.
As explained before, when a user taps the icon of a legitimate app, the malware exploiting Strandhogg vulnerabilities can intercept and hijack this activity/task to display a fake interface to the user instead of launching the real application.
However, unlike StrandHogg 1.0 that can only attack apps one at a time, the latest flaw could let attackers "dynamically attack nearly any app on a given device simultaneously at the touch of a button," all without requiring a pre-configuration for each targeted app.
StrandHogg flaws are potentially dangerous and concerning because:
- it is almost impossible for targeted users to spot the attack,
- it can be used to hijack the interface for any app installed on a targeted device without requiring configuration,
- it can be used to request any device permission fraudulently,
- it can be exploited without root access,
- it works on all versions of Android, except Q.
- it doesn't need any special permission to work on the device.
Besides stealing login credentials through a convincing fake screen, the malware app can also escalate its capabilities significantly by tricking users into granting sensitive device permissions while posing as a legitimate app.
"Utilising StrandHogg 2.0, attackers can, once a malicious app is installed on the device, gain access to private SMS messages and photos, steal victims' login credentials, track GPS movements, make and/or record phone conversations, and spy through a phone's camera and microphone," the researchers said.
"Malware that exploits StrandHogg 2.0 will also be harder for anti-virus and security scanners to detect and, as such, poses a significant danger to the end-user," they added.
Security researchers responsibly reported the new vulnerability to Google in December last year.
After that, Google prepared a patch and shared it with smartphone manufacturing companies in April 2020, who have now started rolling out software updates to their respective users from this month.
Though there is no effective and reliable way to block or detect task hijacking attacks, users can still spot such attacks by keeping an eye on discrepancies we shared while reporting StrandHogg 1.0, like when:
Security researchers responsibly reported the new vulnerability to Google in December last year.
After that, Google prepared a patch and shared it with smartphone manufacturing companies in April 2020, who have now started rolling out software updates to their respective users from this month.
Though there is no effective and reliable way to block or detect task hijacking attacks, users can still spot such attacks by keeping an eye on discrepancies we shared while reporting StrandHogg 1.0, like when:
- an app you're already logged into is asking for a login,
- permission popups that do not contain an app name,
- permissions asked from an app that shouldn't require or need the permissions it asks for,
- buttons and links in the user interface do nothing when clicked on,
- The back button does not work as expected.
THN
#osutayusuf
- Get link
- X
- Other Apps
- Get link
- X
- Other Apps

Comments
Post a Comment