What to Know About it Before You or Your Organisation Becomes Prey To Hackers.
Cloud services have become increasingly important to many companies' daily operations, and the rapid adoption of web apps has allowed businesses to continue operating with limited productivity hiccups, even as global coronavirus restrictions have forced much of the world to work from home.
But at the same time, even major corporations have fallen prey to hackers. How can you maintain the integrity of your IT resources and data while still taking advantage of the benefits of software as a service (SaaS)?
While cybersecurity is a broad and complicated topic, let's consider a hypothetical SaaS scenario and examine some of the risks.
Imagine that one of your employees is writing a sensitive report. It could have financial or medical data in it. It could have information on a revolutionary new design. Whatever it is, the report needs to be kept confidential.
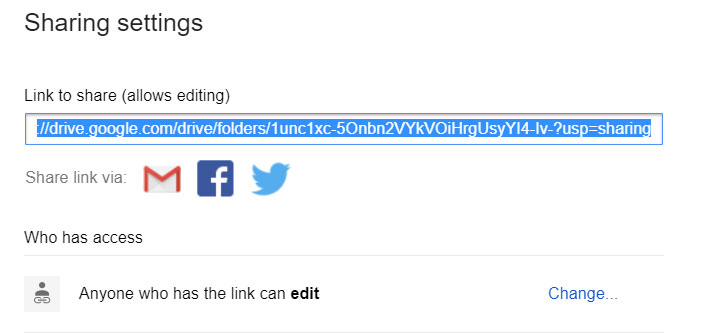
What would happen if your employee writes the report in Google Docs? Let's assume that this decision wasn't run past the IT department. The employee just did it out of habit because Google Docs is what he or she had been using for years to share documents easily with coworkers.
What are some of the risks facing your company?
A key problem that you may face is simply being unaware that the report is in Google Docs. When your IT department doesn't know about the SaaS applications that your team uses, they can't evaluate whether they are safe.
These apps are, therefore, considered shadow IT, tech used without the permission or knowledge of the IT department. The issue, of course, is not about Google.
But at the same time, even major corporations have fallen prey to hackers. How can you maintain the integrity of your IT resources and data while still taking advantage of the benefits of software as a service (SaaS)?
While cybersecurity is a broad and complicated topic, let's consider a hypothetical SaaS scenario and examine some of the risks.
Imagine that one of your employees is writing a sensitive report. It could have financial or medical data in it. It could have information on a revolutionary new design. Whatever it is, the report needs to be kept confidential.
What would happen if your employee writes the report in Google Docs? Let's assume that this decision wasn't run past the IT department. The employee just did it out of habit because Google Docs is what he or she had been using for years to share documents easily with coworkers.
What are some of the risks facing your company?
The problem of unsanctioned applications.
A key problem that you may face is simply being unaware that the report is in Google Docs. When your IT department doesn't know about the SaaS applications that your team uses, they can't evaluate whether they are safe.
These apps are, therefore, considered shadow IT, tech used without the permission or knowledge of the IT department. The issue, of course, is not about Google.
The same problem could occur with a Word document synced through Dropbox or with any number of other legitimate SaaS applications that store data in the cloud. The problem is the lack of visibility.
Shadow IT can be a severe problem, but it often exists because employees lack the right tools. As Harvard Business Review noted, shutting down shadow IT "may at times be an appropriate response, but we have also seen IT adopt an open-minded approach and successfully work with the rogue unit to help secure data, standardize APIs, and ultimately assemble solutions that combine internal and external services. In general, we lean towards the latter approach."
Sometimes the right approach is to secure the applications and make sure that they are used responsibly.
What can you do to improve the sanctioning processes, compliance, and security of your SaaS applications? Aside from doing your due diligence in researching service providers, here are some suggestions.
Passwords are low-hanging fruit. Make sure that everyone in your company has and uses a proper password manager like LastPass or 1Password. You may want to consider requiring hardware security keys like the ones from Yubico. Google has had great success in preventing phishing attacks simply by requiring employees to use physical security keys for two-factor authentication.
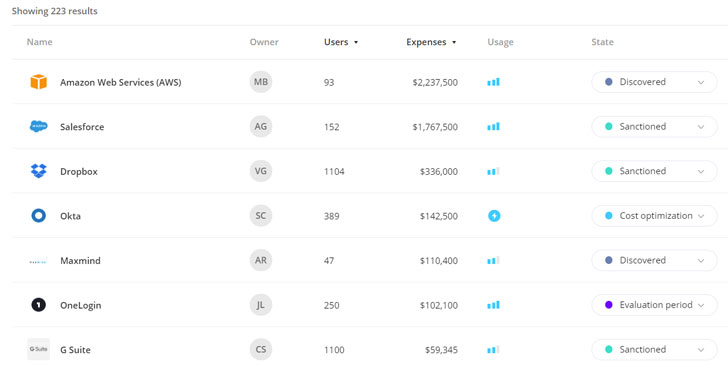
You may also benefit from using a SaaS management tool, especially if you use a large number of software services or have a problem with shadow IT.
Torii, a SaaS management platform, can help you discover and evaluate all of the cloud-based applications used within your organization.
As you add more services, keeping track of what your employees are using, where your money is going, and details like when contracts are up for renewal can help you maintain the security of those services and make sure that you are not overspending or duplicating capabilities.
Torii can help you save money by eliminating waste, but perhaps more importantly, it can give you comprehensive and dynamic visibility of how your organization uses SaaS applications. You can also use it to set up triggered actions for "autonomous SaaS management," like sending a questionnaire to team members who have adopted new apps.
You do, of course, need to evaluate SaaS applications— even officially sanctioned ones—from both an internal perspective and an external view. You need to look at not only your own security practices but also the security practices of the service you are using.
Extremely sensitive data probably should not leave your network, but all personally identifiable information (PII) needs to be handled properly, or you'll risk regulatory compliance issues.
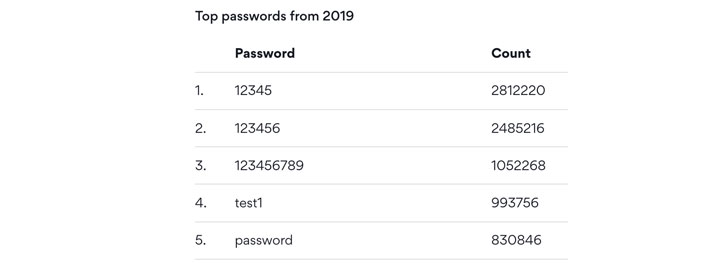
On the internal side, IT departments routinely face problems with bad passwords. Even after years of news reports about serious data breaches, "123456" was still one of the most commonly used passwords in 2019.
And, according to Yubico, a manufacturer of hardware authentication keys, more than two-thirds of employees share passwords and application access with colleagues, while more than half also use the same passwords for both personal and business accounts.
Another potential issue is simply the amount of information that users tend to share with SaaS applications. Many people share calendars and address books readily, and while doing so may be convenient, it also gives that application extra data, data that it may not need for your purposes and data that may be confidential. As with all data, when it comes to SaaS applications, you need to ask where that information is going, how it will be stored, and what the service provider will do with it.
On the external side, even when a SaaS service has seemingly good policies governing its use of your data, code vulnerabilities may still compromise the software. The 2017 Equifax breach, for example, was perpetrated by hackers who exploited a bug in Apache Struts, an open-source web application framework. While a patch for the bug was available, Equifax had not installed it. Without a timely update, Equifax left itself vulnerable to a known problem. As a result, confidential information on about 150 million Americans was lost.
Security is a moving target, and mitigating risk is a never-ending task. While you can never eliminate risk entirely, you can at least reduce it. With basic security steps and careful evaluation of your company's SaaS usage, you can reduce your attack surface and better secure your data.
Shadow IT can be a severe problem, but it often exists because employees lack the right tools. As Harvard Business Review noted, shutting down shadow IT "may at times be an appropriate response, but we have also seen IT adopt an open-minded approach and successfully work with the rogue unit to help secure data, standardize APIs, and ultimately assemble solutions that combine internal and external services. In general, we lean towards the latter approach."
Sometimes the right approach is to secure the applications and make sure that they are used responsibly.
How to improve your SaaS security.
What can you do to improve the sanctioning processes, compliance, and security of your SaaS applications? Aside from doing your due diligence in researching service providers, here are some suggestions.
Passwords are low-hanging fruit. Make sure that everyone in your company has and uses a proper password manager like LastPass or 1Password. You may want to consider requiring hardware security keys like the ones from Yubico. Google has had great success in preventing phishing attacks simply by requiring employees to use physical security keys for two-factor authentication.
You may also benefit from using a SaaS management tool, especially if you use a large number of software services or have a problem with shadow IT.
Torii, a SaaS management platform, can help you discover and evaluate all of the cloud-based applications used within your organization.
As you add more services, keeping track of what your employees are using, where your money is going, and details like when contracts are up for renewal can help you maintain the security of those services and make sure that you are not overspending or duplicating capabilities.
Torii can help you save money by eliminating waste, but perhaps more importantly, it can give you comprehensive and dynamic visibility of how your organization uses SaaS applications. You can also use it to set up triggered actions for "autonomous SaaS management," like sending a questionnaire to team members who have adopted new apps.
Two sides of SaaS security.
You do, of course, need to evaluate SaaS applications— even officially sanctioned ones—from both an internal perspective and an external view. You need to look at not only your own security practices but also the security practices of the service you are using.
Extremely sensitive data probably should not leave your network, but all personally identifiable information (PII) needs to be handled properly, or you'll risk regulatory compliance issues.
On the internal side, IT departments routinely face problems with bad passwords. Even after years of news reports about serious data breaches, "123456" was still one of the most commonly used passwords in 2019.
And, according to Yubico, a manufacturer of hardware authentication keys, more than two-thirds of employees share passwords and application access with colleagues, while more than half also use the same passwords for both personal and business accounts.
Another potential issue is simply the amount of information that users tend to share with SaaS applications. Many people share calendars and address books readily, and while doing so may be convenient, it also gives that application extra data, data that it may not need for your purposes and data that may be confidential. As with all data, when it comes to SaaS applications, you need to ask where that information is going, how it will be stored, and what the service provider will do with it.
On the external side, even when a SaaS service has seemingly good policies governing its use of your data, code vulnerabilities may still compromise the software. The 2017 Equifax breach, for example, was perpetrated by hackers who exploited a bug in Apache Struts, an open-source web application framework. While a patch for the bug was available, Equifax had not installed it. Without a timely update, Equifax left itself vulnerable to a known problem. As a result, confidential information on about 150 million Americans was lost.
Taking charge of your security.
Security is a moving target, and mitigating risk is a never-ending task. While you can never eliminate risk entirely, you can at least reduce it. With basic security steps and careful evaluation of your company's SaaS usage, you can reduce your attack surface and better secure your data.
THN
#osutayusuf
- Get link
- X
- Other Apps
- Get link
- X
- Other Apps

Comments
Post a Comment