Cybersecurity researchers took the wraps off yet another instance of Android malware hidden under the guise of legitimate applications to stealthily subscribe unsuspecting users for premium services without their knowledge.
https://www.facebook.com/1829407613953796
https://www.facebook.com/1829407613953796
In a report published by Check Point research today, the malware — infamously called Joker (or Bread) — has found another trick to bypass Google's Play Store protections: obfuscate the malicious DEX executable inside the application as Base64 encoded strings, which are then decoded and loaded on the compromised device.
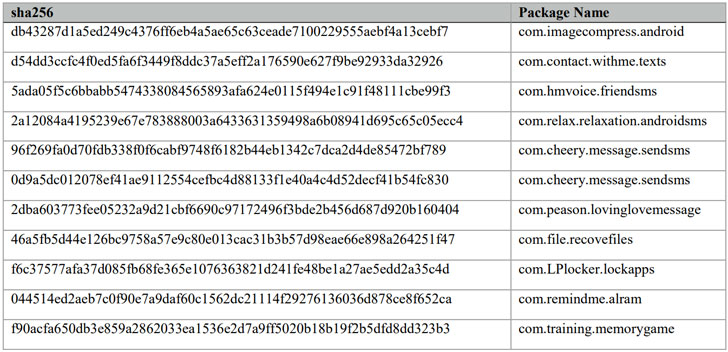
Following responsible disclosure by Check Point researchers, the 11 apps in question were removed by Google from the Play Store on April 30, 2020.
"The Joker malware is tricky to detect, despite Google's investment in adding Play Store protections," said Check Point's Aviran Hazum, who identified the new modus operandi of Joker malware. "Although Google removed the malicious apps from the Play Store, we can fully expect Joker to adapt again."
Joker: A Large-Scale Billing Fraud Family.
First discovered in 2017, Joker is one of the most prevalent kinds of Android malware, notorious for perpetrating billing fraud and its spyware capabilities, including stealing SMS messages, contact lists, and device information.
Campaigns involving Joker gained more foothold last year, with a number of malware-infected Android apps uncovered by CSIS Security Group, Trend Micro, Dr Web and Kaspersky, repeatedly finding unique ways to exploit gaps in Play Store security checks.
To mask their true nature, the malware authors behind the large-scale operation have resorted to a variety of methods — encryption to hide strings from analysis engines, fake reviews to lure users into downloading the apps, and a technique called versioning, which refers to uploading a clean version of the app to the Play Store to build trust among users and then sneakily adding malicious code at a later stage via app updates.
"As the Play Store has introduced new policies and Google Play Protect has scaled defenses, Bread apps were forced to continually iterate to search for gaps," Android's Security & Privacy Team said earlier this year. "They have at some point used just about every cloaking and obfuscation technique under the sun in an attempt to go undetected."
As of January 2020, Google has removed more than 1,700 apps submitted to the Play Store over the past three years that had been infected with the malware.
Using Android Manifest to Hide Malicious DEX File
The new variant spotted by Check Point has the same goal but goes about it by leveraging the app's manifest file, which it uses to load a Base64 encoded DEX file.
A second "in-between" version identified by Check Point employs a similar technique of hiding the .dex file as Base64 strings but adds them as an inner class in the main application and loads it via reflection APIs.
"To achieve the capability of subscribing the users to premium services without their knowledge or consent, the Joker utilized two main components — the Notification Listener as a part of the original application, and a dynamic dex file loaded from the C&C server to perform the registration," Hazum noted in his analysis.
Furthermore, the variant comes equipped with a new feature that allows the threat actor to remotely issue a "false" status code from a C&C server under their control to suspend the malicious activity.
If anything, the latest Joker scheme represents less of a critical threat than it does a reminder of how Android malware is continually evolving and has to be protected continuously.
For users who've installed any of the infected apps, it's worth checking your mobile and transaction history to see if there are any suspicious payments that you don't recognize. Also, make sure to carefully scrutinize your permissions for every app installed on your Android device.
THN
#osutayusuf
- Get link
- X
- Other Apps
- Get link
- X
- Other Apps


Comments
Post a Comment