This Article is Typically For GOOGLE CHROME Users.Update Google Chrome Browser to Patch New Security Flaw, Remote Code Execution Attacks (RCEA).
Google has released an urgent software update for its Chrome web browser and is urging Windows, Mac, and Linux users to upgrade the application to the latest available version immediately.
Started rolling out to users worldwide this Wednesday, the Chrome 77.0.3865.90 version contains security patches for 1 critical and 3 high-risk security vulnerabilities, the most severe of which could allow remote hackers to take control of an affected system.
Google has decided to keep details of all four vulnerabilities secret for a few more days in order to prevent hackers from exploiting them and give users enough time to install the Chrome update.
Started rolling out to users worldwide this Wednesday, the Chrome 77.0.3865.90 version contains security patches for 1 critical and 3 high-risk security vulnerabilities, the most severe of which could allow remote hackers to take control of an affected system.
Google has decided to keep details of all four vulnerabilities secret for a few more days in order to prevent hackers from exploiting them and give users enough time to install the Chrome update.
For now, Chrome security team has only revealed that all four vulnerabilities are use-after-free issues in different components of the web browser, as mentioned below, the critical of which could lead to remote code execution attacks.
The use-after-free vulnerability is a class of memory corruption issue that allows corruption or modification of data in the memory, enabling an unprivileged user to escalate privileges on an affected system or software.
Vulnerabilities Patched By Chrome 77.0.3865.90
Use-after-free in UI (CVE-2019-13685) — Reported by Khalil Zhani.
Use-after-free in media (CVE-2019-13688) — Reported by Man Yue Mo of Semmle Security Research Team.
Use-after-free in media (CVE-2019-13687) — Reported by Man Yue Mo of Semmle Security Research Team.
Use-after-free in offline pages (CVE-2019-13686) — Reported by Brendon Tiszka.
The use-after-free vulnerability is a class of memory corruption issue that allows corruption or modification of data in the memory, enabling an unprivileged user to escalate privileges on an affected system or software.
Vulnerabilities Patched By Chrome 77.0.3865.90
Use-after-free in UI (CVE-2019-13685) — Reported by Khalil Zhani.
Use-after-free in media (CVE-2019-13688) — Reported by Man Yue Mo of Semmle Security Research Team.
Use-after-free in media (CVE-2019-13687) — Reported by Man Yue Mo of Semmle Security Research Team.
Use-after-free in offline pages (CVE-2019-13686) — Reported by Brendon Tiszka.
Google has paid out a total of $40,000 in rewards to Man Yue Mo of Semmle for both the vulnerabilities—$20,000 for CVE-2019-13687 and $20,000 for CVE-2019-13688— While the bug bounties for the remaining two vulnerabilities are yet to be decided.
Successful exploitation of these vulnerabilities could allow an attacker to execute arbitrary code in the context of the browser just by convincing victims into just opening, or redirecting them to, a specially-crafted web-page on the affected Chrome browser, without requiring any further interaction.
Successful exploitation of these vulnerabilities could allow an attacker to execute arbitrary code in the context of the browser just by convincing victims into just opening, or redirecting them to, a specially-crafted web-page on the affected Chrome browser, without requiring any further interaction.
Based on previous discloses, the use-after-free flaw could also lead to sensitive information disclosure, security restrictions bypass, unauthorized actions, and cause denial-of-service conditions—depending on the privileges associated with the application.
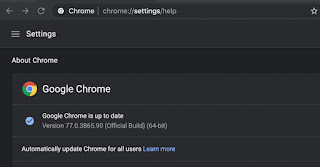
Though Google Chrome automatically notifies users about the latest available version, users are recommended to manually trigger the update process by going to “Help → About Google Chrome” from the menu.
Besides this, you are also recommended to run all software on your systems, whenever possible, as a non-privileged user to diminish the effects of successful attacks exploiting any zero-day vulnerability.
We will update you more about these security vulnerabilities as soon as Google releases their technical details.
Though Google Chrome automatically notifies users about the latest available version, users are recommended to manually trigger the update process by going to “Help → About Google Chrome” from the menu.
Besides this, you are also recommended to run all software on your systems, whenever possible, as a non-privileged user to diminish the effects of successful attacks exploiting any zero-day vulnerability.
We will update you more about these security vulnerabilities as soon as Google releases their technical details.
Comments
Post a Comment